Whenever I'm away from home, I connect to an anonymous proxy VPN to protect my Internet traffic. It's not that I'm doing anything illegal or necessarily anything private, I just don't want to advertise my activity to the entire world.
I pay for this VPN because it's fast and presents me with a wide array of potential data centers through which I can connect. If I'm near home, I connect through a data center in Seattle. If I'm visiting friends on the East Coast, through New York. If traveling abroad, whichever international location yields the highest throughput.
Wherever I am, it means my traffic is safe from inspection regardless who else might be eavesdropping on the network.
Why This Matters
In the earlier days of secure Internet browsing, every secure website could be expected to have a unique IP address. This meant you didn't need to specify the hostname when initiating a TLS handshake to create a secure connection.
As the Internet matured and more sites came online, we quickly exhausted the available address space of the IP protocol.[ref]I'm specifically talking about IPv4 here. The newer IPv6 address space is so large it is unlikely to be exhausted in my lifetime. Unfortunately, support for IPv6 is still ... spotty.[/ref] To get around the limitations, we started hosting multiple sites on the same physical server, reusing the server's IP address. To still route traffic appropriately, we have to leverage Server Name Identification (SNI) and eavesdroppers can intercept unencrypted hostnames.
So anyone looking at the logs will know what sites you're viewing, even if they don't know what pages you're viewing on those sites. For most traffic, this isn't too revealing ... but it's still additional information that can be used to fingerprint an individual based on their web habits.
Where Things Stand Now
https://twitter.com/EricMann/status/786598966850785280
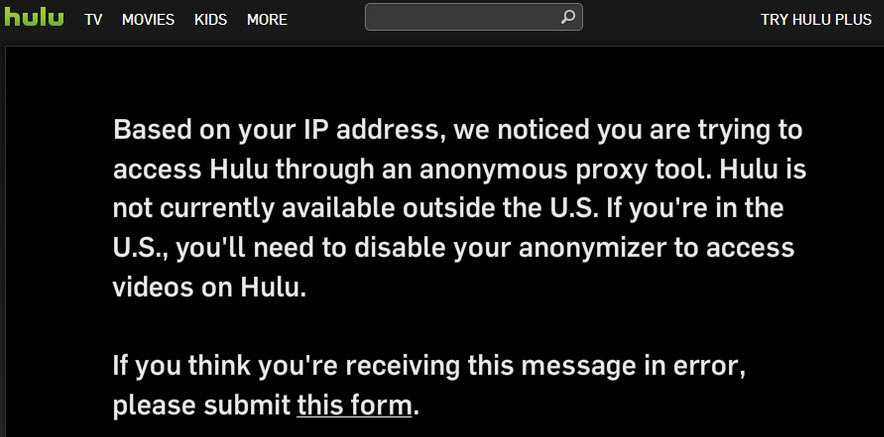
Even using an anonymous proxy is not enough because various media producers - and remember, the web itself is media - are starting to track the IP addresses used by these proxies and is blocking them entirely. Though I'm a paying Hulu subscriber, I can't watch Hulu over my paid VPN.
This past weekend, a friend noticed something curious about one of the news apps he uses. While connected to my home network, the app began displaying intermittent pop-over ads in an attempt to block access to various stories because the publisher detected, and apparently dislikes, my ISP.
Frankly, this behavior is beyond ridiculous.
Solutions
I will still use my paid, anonymous VPN when connecting to various sites as I travel. The bandwidth available is fantastic and, for the small but growing number of sites blocking access, something I can live with for the moment.
For other sites - like Hulu - I have a basic alternative. Thanks to amazing open source projects like Sovereign, I've been able to convert a Raspberry Pi 3 into a private "cloud" server running on my home network.[ref]This is a new build from the one I've documented before. Last time I used a first-generation Pi (which was painfully slow) and was very limited in terms of functionality. The new machine is unparalleled. For example, the Pi 1 took 26 hours to generate a Diffie-Hellman keypair. The Pi 3 took 10 minutes.[/ref] I have a self-hosted ownCloud instance, Git repository server, and most importantly an OpenVPN instance. My machines can now connect securely to my home network and will encrypt any traffic I need remotely, proxying it instead from my home.
It's not the fastest connection in the world, but to any external viewers I'm using the same resources I would be if I were at home on my PC.
I'm also working with a few friends to set up a SoftEther cluster across various datacenters worldwide so we can host our own private replacement for a distributed commercial VPN. Like the commercial option, we would have the ability to connect to whichever node has the fastest speed. Unlike the commercial option, our IP addresses won't be indexed and blocked by media providers.
The point is that the publishing world is becoming increasingly hostile to the notion of personal privacy. These are just some of the steps I'm taking to keep my data secure. What steps are you taking?
